Does your small business have upwards of $100,000 to spend on a preventable issue? Perhaps, but I’m sure you and your leadership team would rather spend that cash on growth. You’ll need to avoid payroll diversion fraud to keep that money in your account.
It’s five past nine o’clock AM on a Friday, and your payroll office phone rings. One employee has noticed that their direct deposit didn’t hit this morning. Your staff notes that the employee just changed their direct deposit info a few days ago. One problem: The employee insists they never requested a change.
Just then, the line rings again.
You’ve racked up a dozen employees within ten minutes with the same issue. You’ve paid them all out… but none of them received funds to their legitimate bank accounts. In other words: you’ve fallen victim to payroll diversion fraud.
Let’s look at three measures you can take to help your organization and your employees avoid falling victim to payroll diversion fraud.
What is Payroll Diversion Fraud?
Cybercriminals have become more creative with how they ‘phish’ for information in the past few years. It’s hard to tell when you’re being scammed: that’s, unfortunately, the point. Payroll diversion fraud is almost too simple. It’s even harder to stop once it starts, and that’s if you even manage to spot it.
Payroll diversion fraud is most typically experienced through cyberphishing: an email scam that falls under the Business Email Compromise umbrella.
In essence, by using a fake email profile and stealing an employee’s login details, cybercriminals trick you into giving them the information they shouldn’t have.
Here’s how it works:
- Infiltration: The scammer infiltrates your system. They target an employee with access to payroll.
- Impersonation: The scammer impersonates an employee, contacts your payroll processor or HR department, and asks them to change their direct deposit information.
- Disbursement: If successful, the scammer receives the payment instead of the employee.
The average cost per attack is $75,000 and represents a real threat to the survival of small businesses.
Related: The Importance of Confidentiality in HR
1. Mandate Employee Education
This type of attack is almost entirely a social engineering attack. Scammers use social media platforms like LinkedIn to observe an organization, identify employees, get their contact information, and plan their attacks.
Related: The Importance of an Employee Handbook
These attacks come across as legitimate and often come from personal email accounts. Attachments might include fake invoices, and subject lines are usually familiar to recipients. In other words, the emails are meant to look like regular emails that payroll and HR personnel are used to dealing with.
But there are tell-tale signs that emails are fake. For example, if an employee emails you from a personal account but their address is johndoe11234, is that normal? Do they use a sense of urgency that doesn’t add up? You can train payroll staff to look for inconsistencies. Question everything!
Pro tip: Implement a verification protocol that ensures the employee requests the change.
You should also train employees to look for red flags. For example, they should never share login credentials via email or phone.
2. Implement Multi-Factor Authentication
MFA (Multi-Factor Authentification) is the process of creating a combination of two or more authenticators to verify your identity. For example, you might log in to a server with your email address, but you’ll also need to enter a code sent to your smartphone before being let in.
How can this measure help? Requiring MFA makes it more challenging for cybercriminals to access an employee’s account or email to request to change their payroll data in the first place.
Remote work is growing in popularity. Every remote employee should create two forms of authentication to log in to work-related websites and portals. This includes employee logins during off-hours. Employees on alternate schedules need access to your servers, but using MFA ensures additional security during remote or off-hours work.
Pro tip: Limit access to payroll and personnel records to the people who need them to do their jobs. Review and update access regularly.
3. Require Identification For Data Changes
How do you make changes to employee information or payroll? You need to review your policies and procedures to ensure they’re safe and effective. Don’t respond to an email or call the number provided in the email. Call the employee using the number in your internal employee directory.
This simple step should be the first line of defense. It almost takes human error out of the equation. If employees have to provide identification to change their direct deposit or banking information, it’s more challenging to access for would-be cybercriminals.
You’ll need to ensure your company’s payroll procedures and policies aren’t available to the public and that employees never share details. For easy verification, you can talk to employees in person, by calling them or using instant message.
Avoiding Payroll Diversion Fraud
By following the three tips outlined above, you should be able to avoid the struggles associated with falling prey to payroll diversion fraud. Education and technology are your best defenses against this type of scam. Ensure you are using everything at your disposal to keep your employees’ data safe.
However, payroll diversion fraud is only the tip of the iceberg concerning payroll-related challenges.
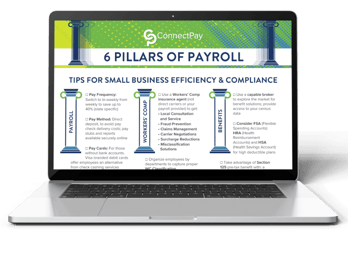
You need experience and knowledge related to Workers’ Comp, payroll taxes, and more to maintain payroll compliance and run your business smoothly. For information on all these topics and more, check out our free reference, the Connected Guide to Small Business Payroll!
With our Connected Guide, you’ll have all the baseline information you need to set up and maintain efficient, painless payroll processes for your business.